Office 365 Graph API set up with Area 1
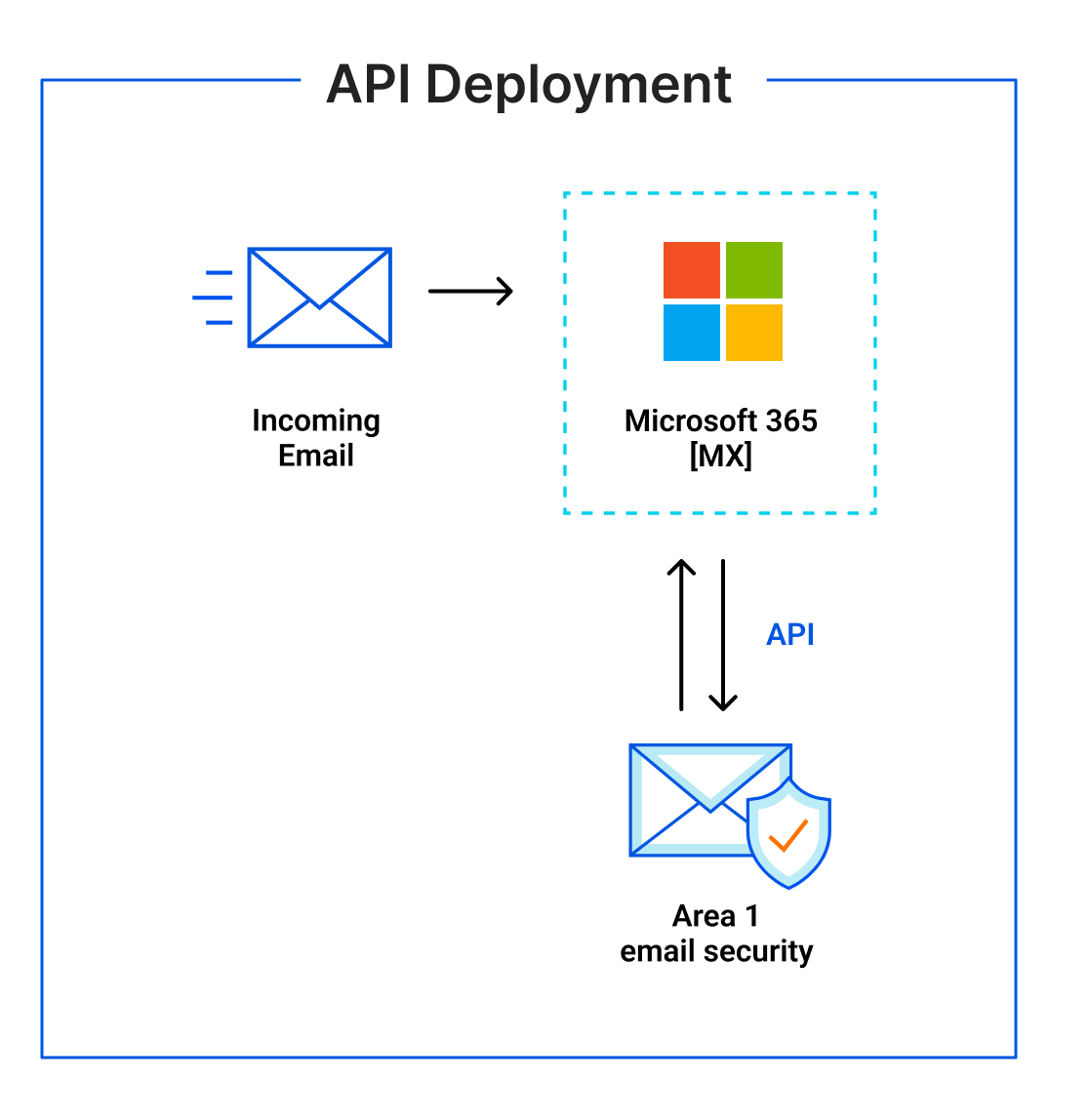
For customers using Microsoft Office 365, setting up Area 1 via Microsoft Graph API is quick and easy. The following email flow shows how this works:
User roles
Area 1 uses two roles for retraction and directory integration purposes:
- Privileged authentication administrator: Users with this role can view the current authentication method information and set or reset non-password credentials for all users, including global administrators. Privileged authentication administrators can force users to re-register against existing non-password credentials (like MFA or FIDO) and revoke the
remember MFA on the devicemessage prompting for MFA on the next login of all users. - Privileged role administrator: Users with this role can manage role assignments in Azure Active Directory, as well as within Privileged Identity Management. In addition, this role allows management of all aspects of Privileged Identity Management.
Directory Integration requires the use of both roles mentioned above. Email retraction only requires the Privileged role administrator. Any Azure administrator with a membership in the required role can perform these authorizations. The authorization process grants the Area 1 dashboard access to the Azure environment. This access is performed with the least applicable privileges required to function, as shown in the table below.
The Enterprise Applications that Area 1 registers are not tied to any administrator account. Inside of the Azure Active Directory admin center you can review the permissions granted to each application in the Enterprise Application section. Refer to Application management documentation for more information.
Set up Microsoft Graph API
Log in to the Area 1 dashboard.
Go to Settings (the gear icon).
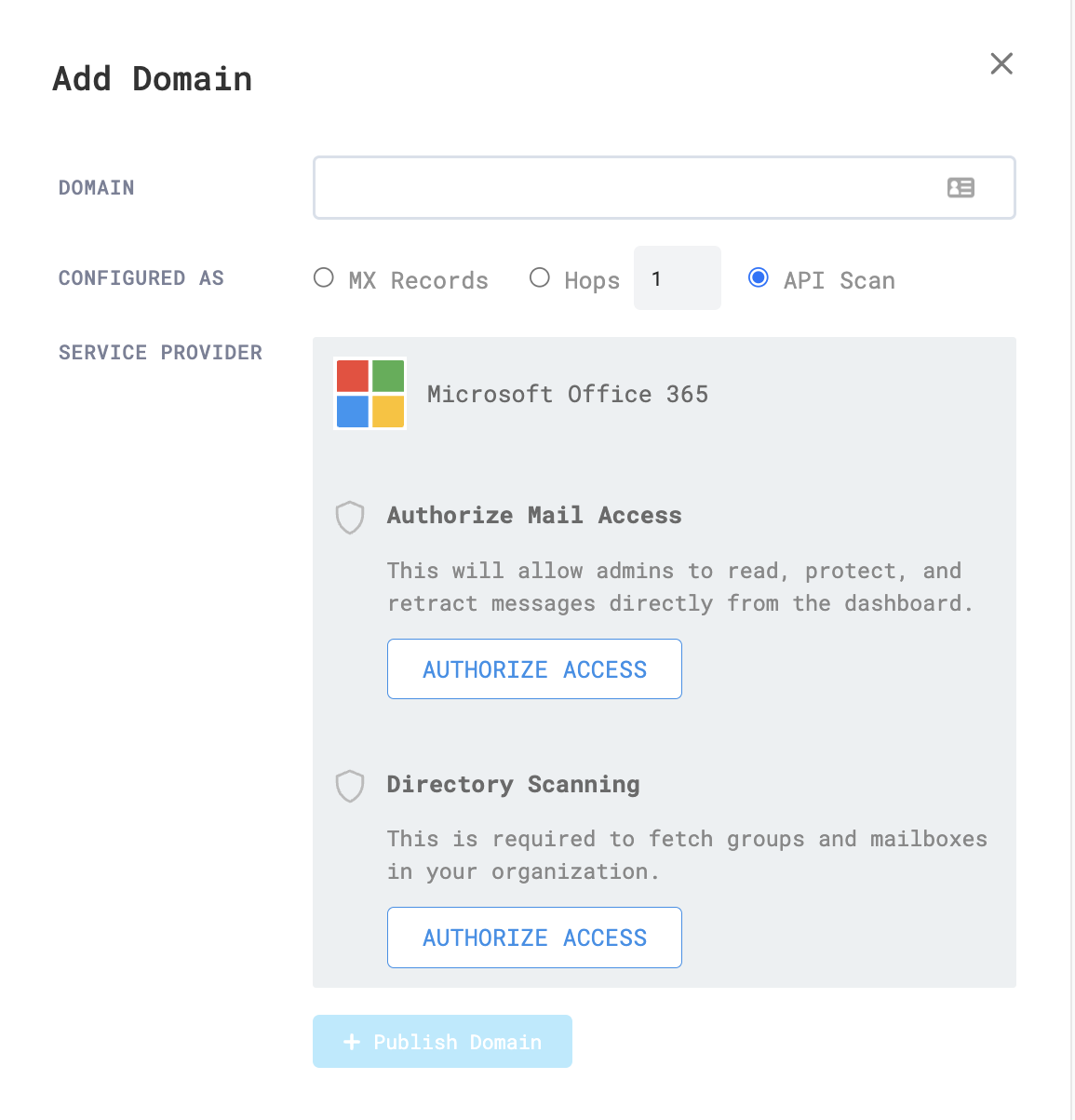
In Email Configuration > Domains & Routing > Domains, select New Domain.
In Domain, enter the domain you want to onboard.
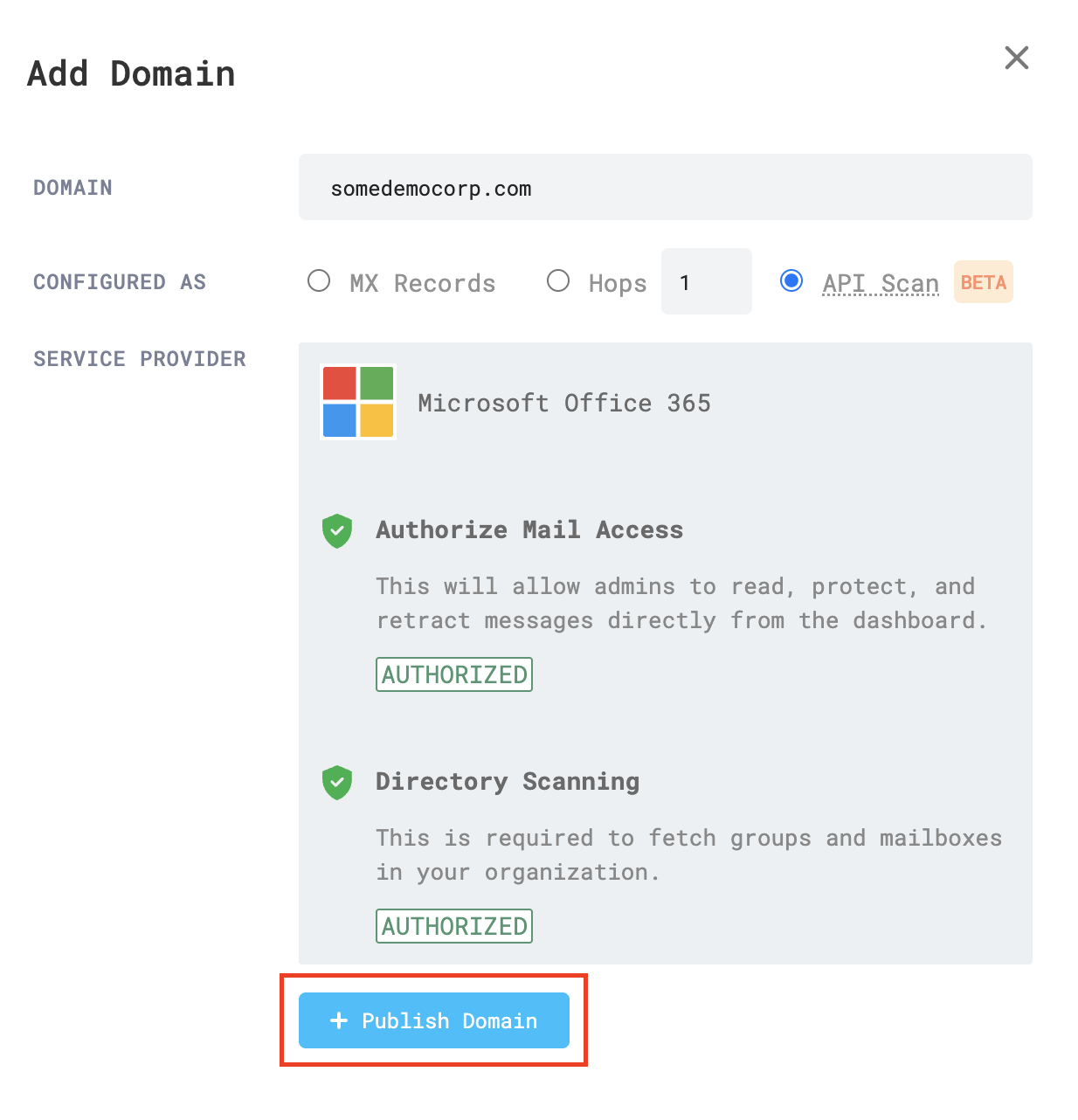
In Authorize Mail Access, select Authorize Access.
In the new tab that opens, choose an Office 365 account you want to authorize, or enter your credentials.
Read the permissions, and select Accept to continue. You will be directed back to the Area 1 dashboard.
In Directory Scanning, select Authorize Access.
In the new tab that opens, choose an Office 365 account you want to authorize, or enter your credentials.
Read the permissions, and select Accept to continue. You will be directed back to the Area 1 dashboard.
Now that both types of authorizations have been complete, select Publish Domain.
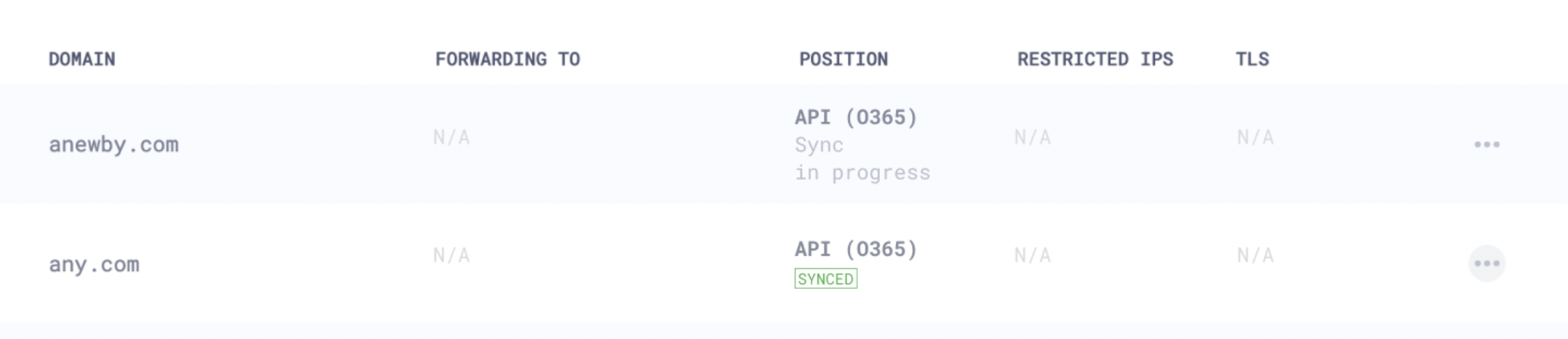
Your authorized domain will show up in Email Configuration > Domains & Routing > Domains, with messages about the progress of directory syncing between Office 365 and Area 1.
Azure applications
Directory Integration
The following table shows API permissions required for Directory Integration as it appears in Azure Enterprise applications.
| API Name | Claim value | Permission | Type | Granted through | Granted by |
|---|---|---|---|---|---|
| Microsoft Graph | User.Read | Sign in and read user profile | Delegated | Admin consent | An administrator |
| Microsoft Graph | Group.Read.All | Read all groups | Application | Admin consent | An administrator |
| Microsoft Graph | Directory.Read.All | Read directory data | Application | Admin consent | An administrator |
| Microsoft Graph | User.Read.All | Read all users’ full profiles | Application | Admin consent | An administrator |
| Microsoft Graph | GroupMember.Read.All | Read all group memberships | Application | Admin consent | An administrator |
Retraction
The following table shows retractions as they appear in Azure Enterprise applications.
| API Name | Claim value | Permission | Type | Granted through | Granted by |
|---|---|---|---|---|---|
| Microsoft Graph | Mail.ReadWrite | Read and write mail in all mailboxes | Application | Admin consent | An administrator |
| Microsoft Graph | Group.Read.All | Read all groups | Application | Admin consent | An administrator |
| Microsoft Graph | User.Read.All | Read all users’ full profiles | Application | Admin consent | An administrator |
| Microsoft Graph | Domain.Read.All | Read domains | Application | Admin consent | An administrator |
| Microsoft Graph | GroupMember.Read.All | Read all group memberships | Application | Admin consent | An administrator |
| Microsoft Graph | Organization.Read.All | Read organization information | Application | Admin consent | An administrator |