Test DNS filtering
This section covers how to validate your Gateway DNS configuration.
Prerequisites
Before you start, make sure you are connected to a network that is associated with the DNS location where the policy is applied.
Test a DNS policy
Once you have created a DNS policy to block a domain, you can use either dig or nslookup to see if the policy is working as intended.
For example, if you created a policy to block example.com, you can do the following to see if Gateway is successfully blocking example.com:
Open your terminal.
Type
dig example.com(nslookup example.comif you are using Windows) and press Enter.If the block page is disabled for the policy, you should see
REFUSEDin the answer section: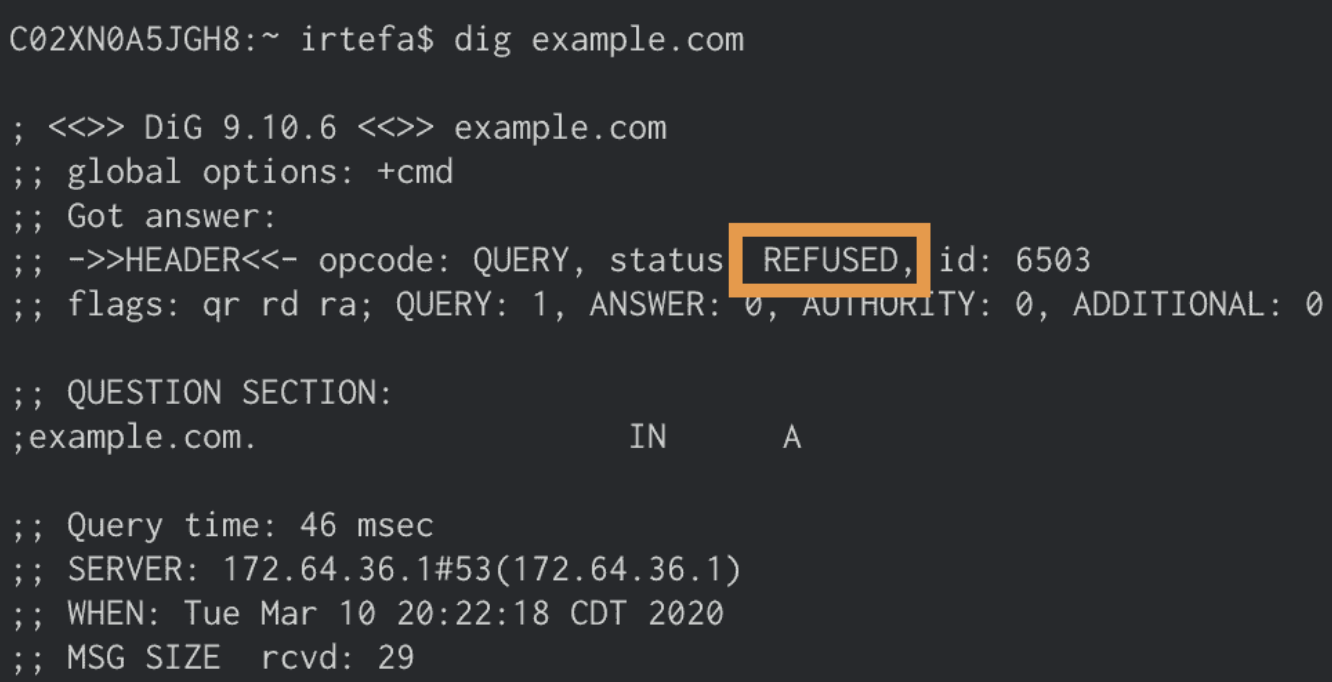
If the block page is enabled for the policy, you should see
NOERRORin the answer section and162.159.36.12and162.159.46.12as the answers: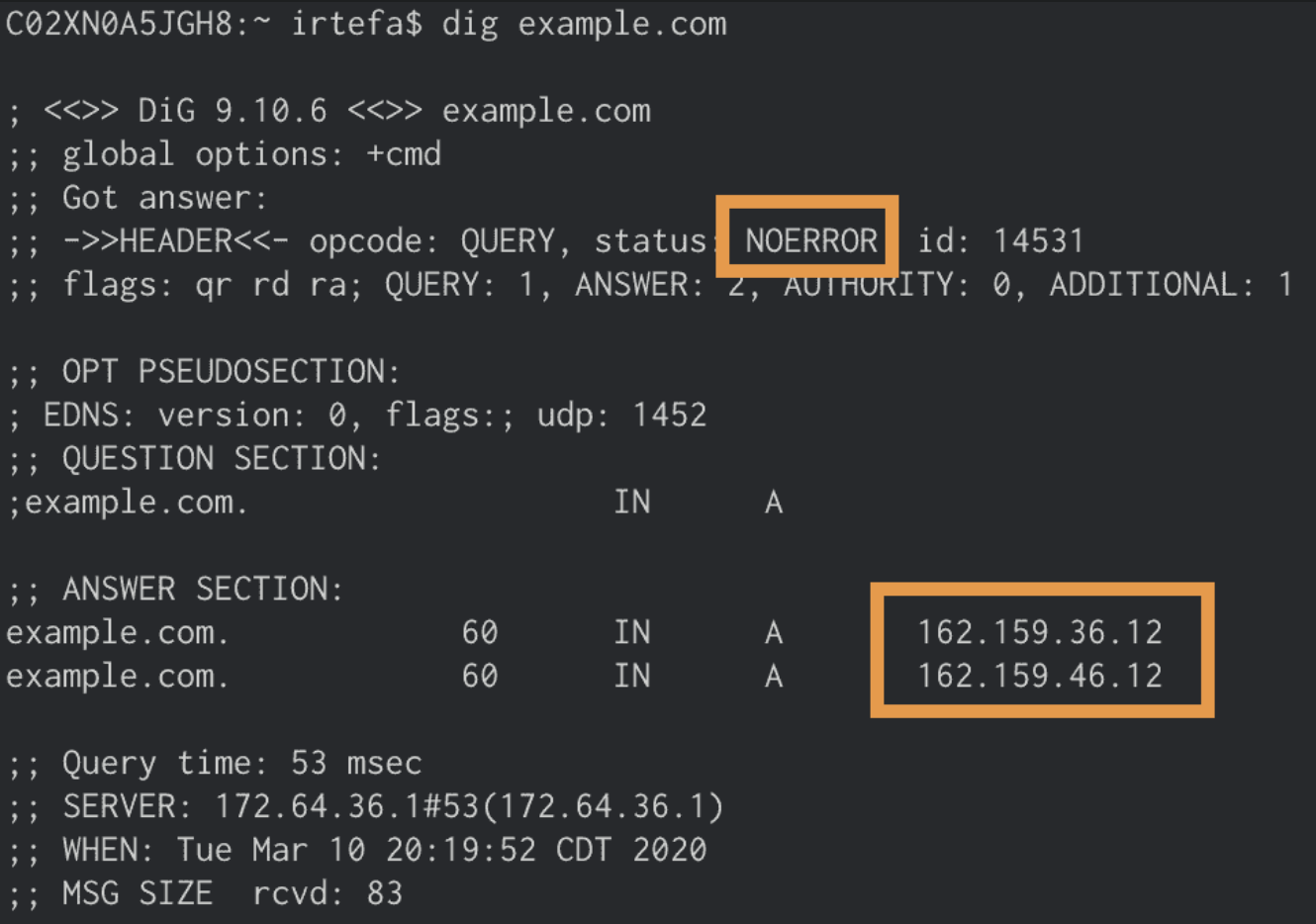
Test a security or content category
If you are blocking a security category or a content category, you can test that the policy is working by using the test domain associated with each category.
Once you have configured your Gateway policy to block the category, the test domain will show a block page when you attempt to visit the domain in your browser, or will return REFUSED when you perform dig using the command-line interface.
Test domain format
One-word category — For categories with one-word names (for example, Malware), the test domain uses the following format:
<NAME_OF_CATEGORY>.testcategory.comMulti-word category — For categories with multiple words in the name (for example, Parked & For Sale Domains), the test domain uses the following format:
- Remove any spaces between the words
- Replace
&withand - Lowercase all letters
Common test domains
| Category | Test domain |
|---|---|
| Anonymizer | anonymizer.testcategory.com |
| Command and Control & Botnet | commandandcontrolandbotnet.testcategory.com |
| Cryptomining | cryptomining.testcategory.com |
| Malware | malware.testcategory.com |
| New Domains | newdomains.testcategory.com |
| Parked & For Sale Domains | parkedandforsaledomains.testcategory.com |
| Phishing | phishing.testcategory.com |
| Private IP Address | privateipaddress.testcategory.com |
| Spam | spam.testcategory.com |
| Spyware | spyware.testcategory.com |
| Unreachable | unreachable.testcategory.com |
Test EDNS configuration
If you enabled EDNS client subnet for your DNS location, you can validate EDNS as follows:
Obtain your DNS location’s DOH subdomain:
- In Zero Trust, go to Gateway > DNS Locations.
- Select the DNS location you are testing.
- Note the value of DNS over HTTPS.
Open a terminal and run the following command:
$ curl 'https://<DOH_SUBDOMAIN>.cloudflare-gateway.com/dns-query?type=TXT&name=o-o.myaddr.google.com' -H 'Accept: application/dns-json' | json_ppThe output should contain your EDNS client subnet:
{"AD" : false,"Answer" : [{"TTL" : 60,"data" : "\"108.162.218.211\"","name" : "o-o.myaddr.google.com","type" : 16},{"TTL" : 60,"data" : "\"edns0-client-subnet 136.62.0.0/24\"","name" : "o-o.myaddr.google.com","type" : 16}],"CD" : false,"Question" : [{"name" : "o-o.myaddr.google.com","type" : 16}],"RA" : true,"RD" : true,"Status" : 0,"TC" : false}To verify your EDNS client subnet, obtain your source IP address:
$ curl ifconfig.me136.62.12.156%The source IP address should fall within the /24 range specified by your EDNS client subnet.